General Details for Data Centers Perimeter Security
Data center perimeter security provides a robust, multi-layered defense to protect mission-critical facilities, digital assets, and supporting infrastructure from unauthorized access, intrusion, sabotage, and physical threats. It combines high-security fencing or reinforced boundary walls with anti-climb and anti-dig measures, integrated with fiber-optic–based Perimeter Intrusion Detection Systems (PIDS) that deliver real-time, high-accuracy detection of cutting, climbing, tampering, and ground disturbance with minimal false alarms. The solution is further strengthened by intelligent video surveillance, strictly controlled access points, and centralized security management systems, ensuring continuous situational awareness, rapid incident response, operational continuity, and compliance with data protection, regulatory, and industry security standards.
FOL-101
Securing Fences & Buried Perimeter for Data Center


Securing the perimeter is the first and most critical layer of physical protection for data centers, hyperscale facilities, cloud campuses, and mission-critical IT infrastructure sites. The FOL-101 Fence and Buried Perimeter Intrusion Detection System provides continuous, real-time monitoring of both perimeter fences and underground boundaries using advanced fiber-optic sensing technology. The system is specifically designed to prevent unauthorized access, trespassing, theft, vandalism, sabotage, and intrusion attempts at sensitive data center environments. It reliably detects fence climbing, cutting, pulling, lifting, and tampering, as well as digging or ground disturbance near the data center boundary — before any security breach occurs. With high detection accuracy and extremely low nuisance alarms, FOL-101 ensures reliable, 24×7 protection for data centers, helping safeguard critical IT assets, maintain operational continuity, and support compliance with stringent security standards.
How the Fence and Buried Perimeter Security Works?
A fiber-optic sensing cable is installed on the perimeter fence and/or buried underground along the data center boundary. The perimeter is divided into Zone 1 to Zone 8, each covering up to 500 m range. Any physical disturbance on the fence or ground generates an instant alarm. The controller identifies the exact zone of intrusion, and alarms are transmitted to the central control room for immediate response.
Zone-Based Alarm Detection
- Exact intrusion location displayed zone-wise
- Multiple intrusions can be detected simultaneously in different zones
- Reduces response time and improves operational efficiency
- Ideal for data centers, server campuses, colocation facilities, and restricted IT zones
Key Advantages for Data Center Security
- Early intrusion detection before perimeter breach
- Extremely low nuisance alarms with 24×7 reliable security
- No electrical power required on the fence
- Immune to EMI, radiation-safe, lightning, and extreme weather conditions
- Centralized monitoring from the data center control room or remote monitoring facility
FR-201
Securing Fences & Buried Perimeter for Data Center
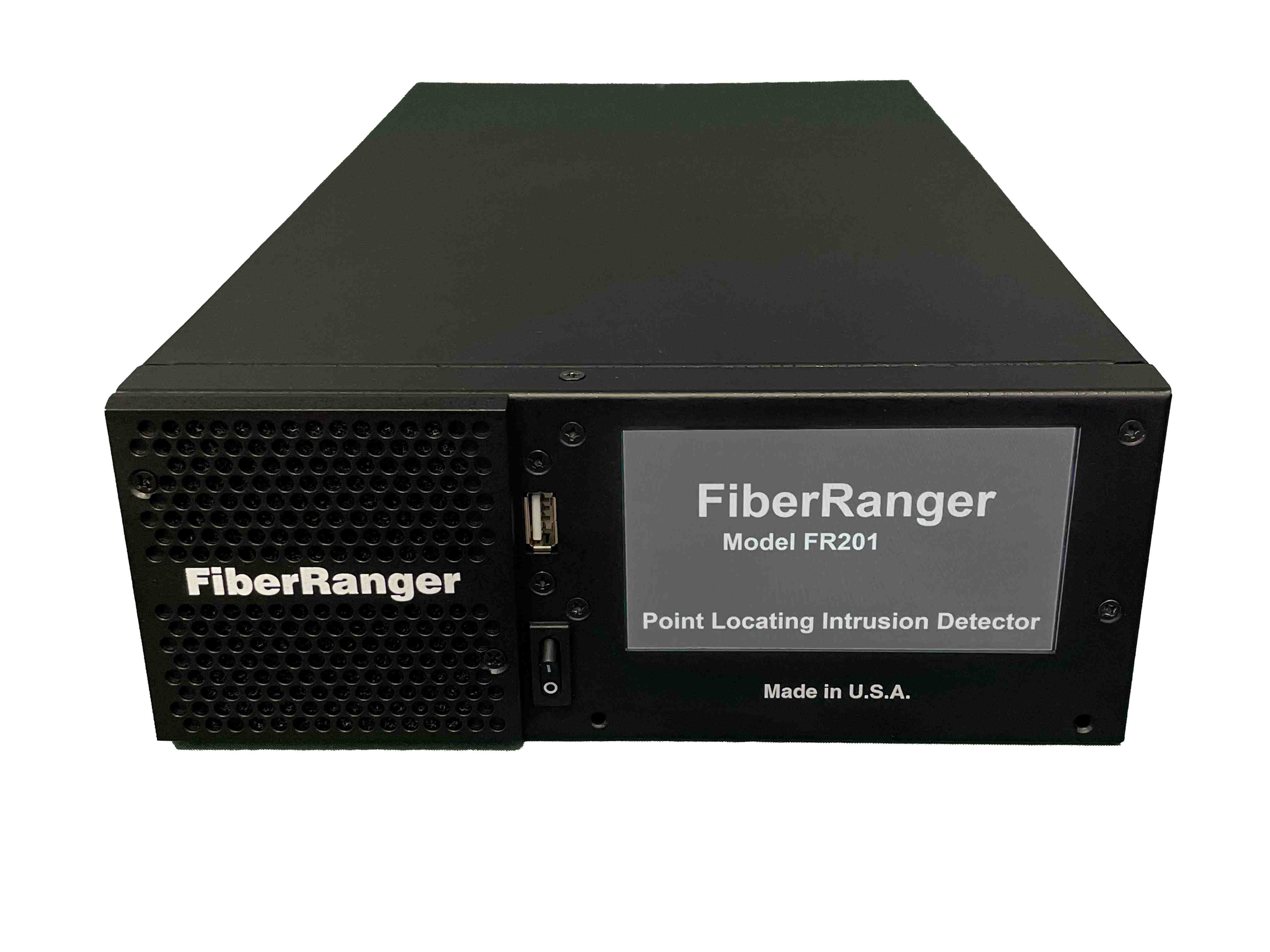

FR-201 is a point-locating Fiber Optic Intrusion Detection System designed to protect data centers, hyperscale facilities, colocation campuses, and mission-critical IT infrastructure. Data centers require multi-layered, highly reliable perimeter security to prevent unauthorized access, theft, vandalism, sabotage, and covert intrusion attempts such as digging or boundary breaches near sensitive IT and network assets. The FR-201 provides continuous, real-time monitoring of both perimeter fencing and buried boundaries using advanced fiber-optic sensing technology. The system is engineered to detect, classify, and precisely locate attempts to breach the secured perimeter — including fence attacks, ground disturbance, digging, or tunneling — well before a security breach occurs, enabling immediate and targeted response to protect critical data and infrastructure.
How the System Works?
A fiber-optic sensing cable (single mode) is installed on the perimeter fence or buried underground along the data center. The same sensing cable can protect fence and buried together. Any disturbance creates a signal that is analyzed by the FR-201 controller. The system generates a pinpoint location alarm within a few meters. The exact intrusion point is displayed on the monitoring system. This allows security teams to respond quickly and accurately to real threats.
Fence Intrusion Detection
- Climbing
- Cutting
- Pulling or lifting of the fence
- Fence tampering
Buried Perimeter Detection
- Digging
- Tunneling
- Ground disturbance near walls, foundations, or cable trenches
- Covert intrusion attempts
Pinpoint Location Alarms
- Intrusion location accuracy within a few meters
- Supports multiple simultaneous intrusion events
Integration
- Alarm data available via: TCP/IP (XML, ASCII, Modbus) or Relay outputs
- Can automatically trigger PTZ cameras, Hooters, Flood lights
Key Advantages for Data Center Security
- Early detection before breach
- Alarms are shown on the map with precise meter location and GPS coordinates
- Extremely low nuisance alarms with 24×7 reliable security due to intelligent pattern recognition algorithms
- No electrical power in the field
- Immune to EMI, lightning, and weather conditions
- Cut-immune configuration — system remains operational even if cable is cut
- High reliability for mission-critical and high-availability data center environments
- Centralized monitoring from the Data Center Security Operations Center (SOC), command center, or remote monitoring facility
- Precise location of the intrusion, which can accurately trigger a camera

