General Details for Critical Infrastructures Perimeter Security
Critical infrastructure perimeter security is a multi-layered protection system designed to prevent unauthorized access, sabotage, theft, and operational disruption across high-value and sensitive facilities. It integrates reinforced perimeter barriers with fiber-optic–based Perimeter Intrusion Detection Systems (PIDS) for real-time detection of intrusion, tampering, and ground disturbances. Combined with intelligent surveillance, secure access control, and centralized monitoring, the system ensures continuous protection, rapid response, operational continuity, and enhanced safety of critical assets and infrastructure.
FOL-101
Securing Critical Infrastructure Perimeter


Securing the perimeter is essential for protecting critical infrastructure facilities such as power plants, utilities, data centers, transportation hubs, and other high-value national assets. The FOL-101 Perimeter Intrusion Detection System provides continuous, real-time monitoring of fences, walls, and buried perimeters using advanced fiber-optic sensing technology.
The system is specifically designed to detect unauthorized access, sabotage, vandalism, and intrusion attempts, including climbing, cutting, tampering, vibration, digging, and tunneling activities near the perimeter — before a breach occurs. With high detection accuracy and extremely low nuisance alarms, FOL-101 delivers reliable security for mission-critical environments where safety and operational continuity are vital.
How the Perimeter Security Works
A fiber-optic sensing cable is installed on the perimeter fence, wall top, or buried underground along the facility boundary. The perimeter is divided into Zone 1 to Zone 8, each covering up to 500 m range. Any physical disturbance or ground vibration generates an instant alarm. The controller identifies the exact zone of intrusion, and alarms are transmitted to the central control room for immediate response.
Zone-Based Alarm Detection
- Exact intrusion location displayed zone-wise
- Multiple intrusions can be detected simultaneously across different zones
- Faster response time and improved operational efficiency
- Ideal for high-security and mission-critical infrastructure areas
Key Advantages for Critical Infrastructure Security
- Early intrusion detection before perimeter breach
- Extremely low nuisance alarms with 24×7 reliable monitoring
- No electrical power required on perimeter installation
- Immune to EMI, lightning, and harsh environmental conditions
- Centralized monitoring from a secure control room
FR-201
Securing Fence and Buried Perimeter for Critical Infrastructure
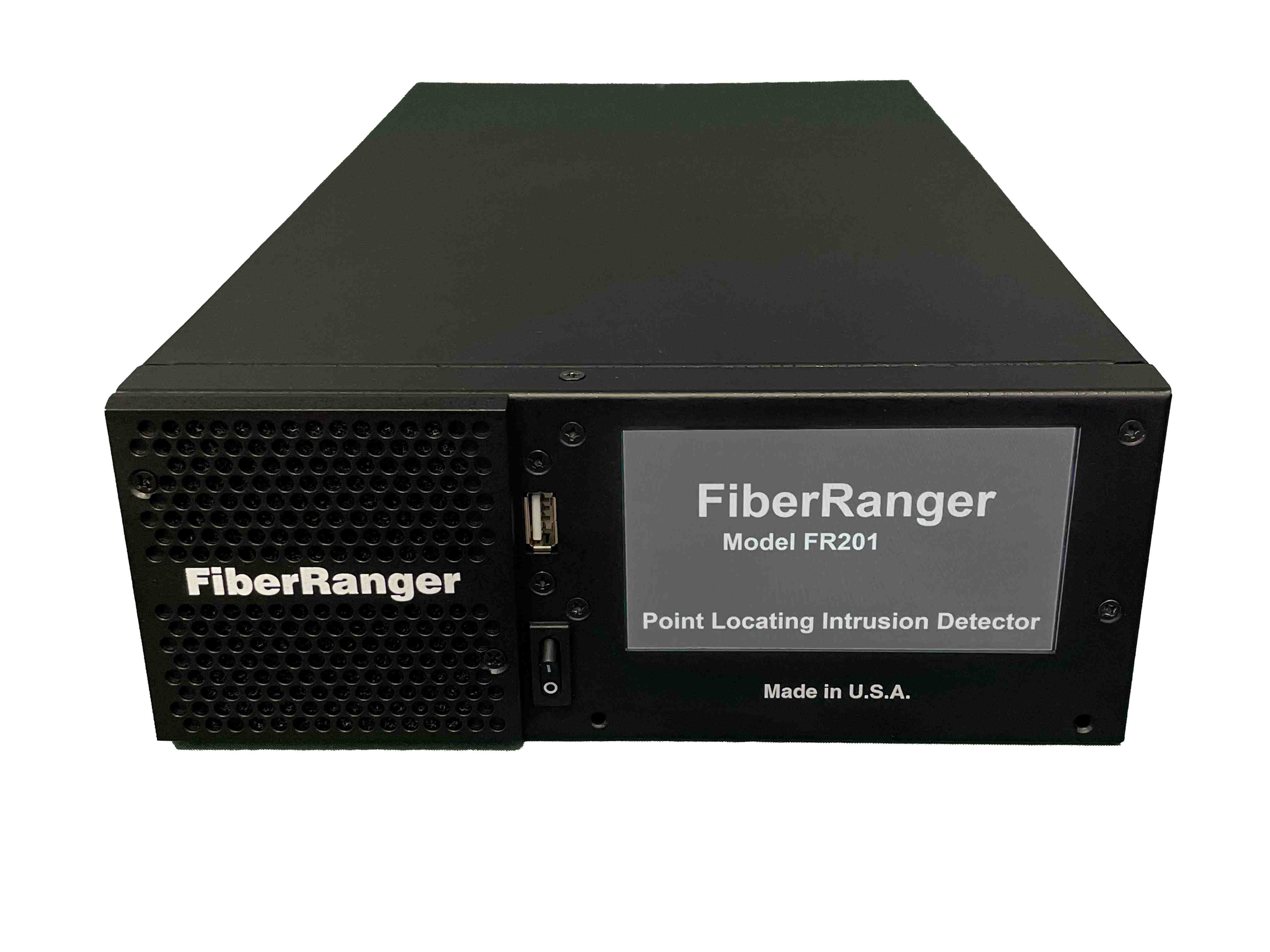

FR-201 is a point-locating Fiber Optic Intrusion Detection System designed to secure critical infrastructure facilities such as power plants, utilities, data centers, transportation hubs, and other mission-critical assets. These sites require layered, fail-safe perimeter protection to prevent unauthorized access, sabotage, infiltration, and coordinated intrusion attempts.
The FR-201 provides continuous, real-time monitoring of both perimeter fence lines and buried perimeters using advanced fiber-optic sensing technology. The system is engineered to detect, classify, and precisely locate intrusion attempts such as fence climbing, cutting, pulling, digging, or tunneling — before the perimeter is breached — enabling rapid and decisive security response.
How the System Works
A single-mode fiber-optic sensing cable is installed on the perimeter fence and/or buried underground along the critical infrastructure boundary. The same sensing cable can protect both fence and buried perimeters simultaneously. Any physical disturbance generates a signal that is analyzed by the FR-201 controller. The system produces a pinpoint location alarm within a few meters, and the exact intrusion point is displayed on the monitoring interface, allowing security teams to respond quickly and accurately to real threats.
Fence Intrusion Detection
- Climbing
- Cutting
- Pulling or lifting of the fence
- Fence tampering
Buried Perimeter Detection
- Digging
- Tunneling
- Ground disturbance near walls or foundations
- Covert intrusion attempts
Pinpoint Location Alarms
- Intrusion location accuracy within a few meters
- Supports multiple simultaneous intrusion events
Integration
-
Alarm data available via:
- TCP/IP (XML, ASCII, Modbus)
- Relay outputs
-
Can automatically trigger:
- PTZ cameras
- Hooters
- Flood lights
Key Advantages for Critical Infrastructure Security
- Early detection before perimeter compromise
- Alarms displayed on maps with precise meter location and GPS coordinates
- Extremely low nuisance alarms using intelligent pattern-recognition algorithms
- No electrical power required in the field
- Immune to EMI, lightning, and harsh environmental conditions
- Cut-immune configuration — system remains operational even if the cable is cut
- High reliability for mission-critical infrastructure facilities
- Centralized monitoring from a secure command & control room
- Precise intrusion location enabling accurate camera triggering

